Introduction to ControlLogix over the Internet
In this section, I’ll show you how easy it is to connect to a ControlLogix system over the Internet without proper security. Undoubtedly, using this procedure will cause a severe security threat. The purpose of this to show how easy a simple change in your router allows access from the outside world. It’s your responsibility to research what security measures work best for you. Never use this exact procedure on production equipment, and add security measures even for training equipment. A VPN or configurable firewall would be a couple options for security. To be clear, I’m not saying this is a security flaw with ControlLogix. This is simply a security concern for ANY device that you allow remote access to. Knowing how to connect to a system behind a router will help you to decide on security measures to take.
Additionally, this procedure will work on other processors, such as a SLC 5/05 or PLC-5 on Ethernet.
Check your Internet IP
Before starting, let’s see if I have a public IP address. The easiest way to do this is to visit a web server that tells us what IP address it sees. After that, I can check my main router to see if it has the same IP address. That will tell me if my router has a public IP address, or if the ISP is shielding and re-distributing IP addresses through NAT. For this to work, I want them to be the same. One website to check this is http://whatismyipaddress.com.
Let’s say this website shows my address as 50.116.19.134.
At this time, I’ll check the IP address that my router has on it’s WAN port. I’ll go to the configuration page of the main router. Of course, for security reasons, I’ve manipulated the image below.
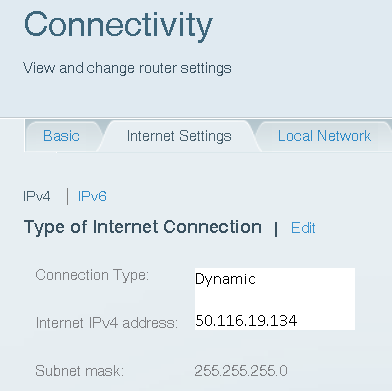
If these match, we are in good shape to continue!
Set up routing to the ControlLogix Ethernet Module
At this time, we are ready to set up the routing. I’m going to look at my ControlLogix ENBT module, and the IP address scrolls across the alphanumeric display. In this case, my IP address of the ENBT is 192.168.1.17.
Most routers have a DMZ (Demilitarized Zone) setting. If not, then just forward port 44818 to your ENBT module. By comparison, this is port 2222 for older AB equipment such as the 5/05.
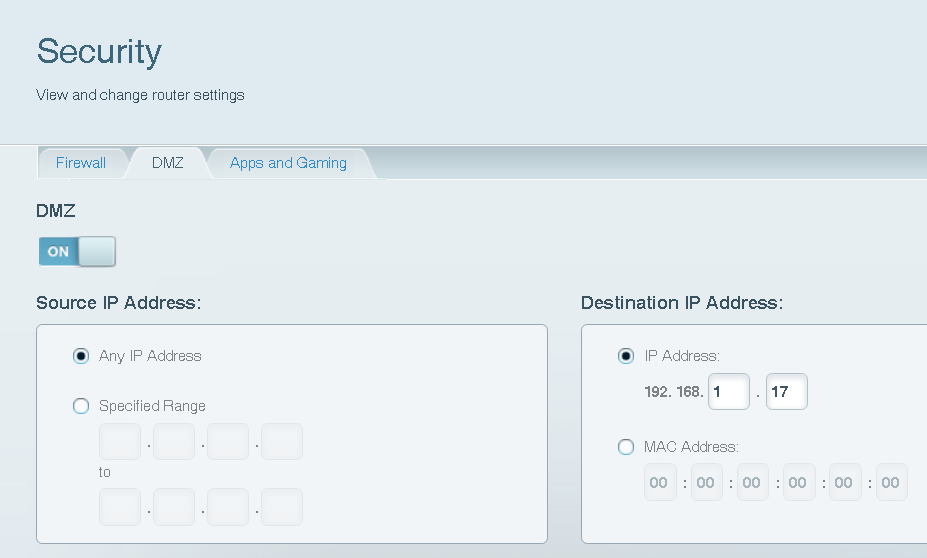
Always remember that anyone with your IP address, and the right software has access to your processor now. As I have said, never implement this on production equipment without additional security. If you know what IP address you are using remotely, you could select a source IP Address as a partial security measure.
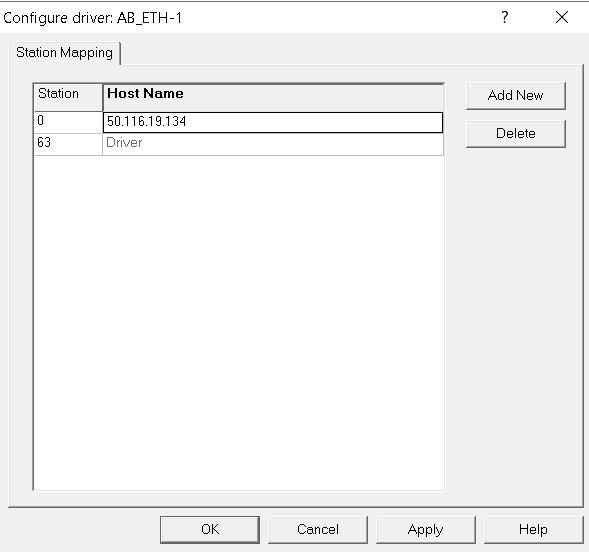
Configure the driver in RSLinx
In RSLinx (From a remote location), go to Communication | Configure Drivers, and select the “Ethernet Devices” Driver. Simply add the IP address of your router’s WAN port as the hostname.
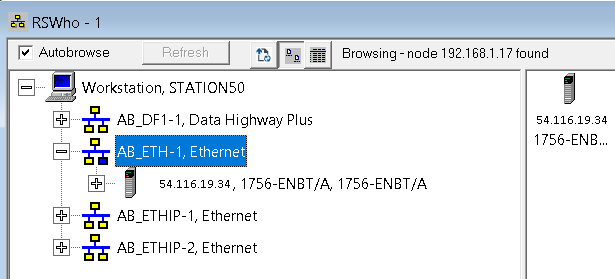
At last, go to RSWho to verify communication to your processor.
Summary
All things considered, as long as your IP address is already public, there is only one change that will allow public access to any device on your network — The DMZ’s Ip Address. For production equipment, it’s best not to have any physical access to the Internet. The reality, however, is that many engineers are now traveling, and many stations are now unmanned. You must weigh the convenience of remote access against security threats, and legal regulations.
For more information on ControlLogix, visit the category page!
— Ricky Bryce
